Beyond the Cashless Society: IBM's Vision for the Future
by Brandon Turbeville
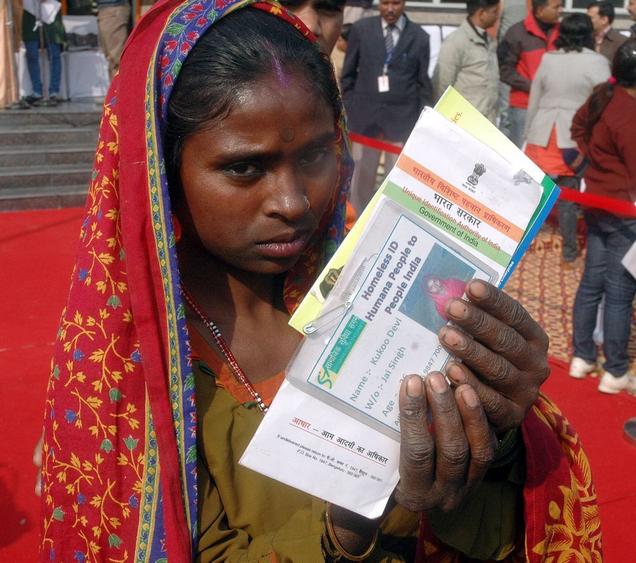
Fresh on the heels of India’s massive databasing program that is set to encompass all 1.2 billion members of its population, recent announcements by IBM should be drawing the attention of some 300 million Americans.
IBM’s “IBM 5 in 5” predictions reveal part of a goal that has been discussed for some time, yet too often continues to be dismissed as mere conspiracy theory. This goal is for biometric data such as fingerprints, iris scans, and voice recognition to not only become commonplace amongst the general public, but soon to replace all other forms of identification.
Even more startling, the next level of technology is set for release which will link the human brain directly to the digital world, enabling the user to control their reality purely by thought.
Even more startling, the next level of technology is set for release which will link the human brain directly to the digital world, enabling the user to control their reality purely by thought.
IBM has also announced that it is developing technology that can harness the power of human movement for the purpose of providing “renewable energy.”
The IBM 5 in 5 is a series of five predictions for the next five years which “is based on market and societal trends as well as emerging technologies from IBM’s research labs around the world that can make these transformations possible.”
Directly related to the massive biometric database being created in India, the IBM technology can (and most likely will) be used to create a database of user biometrics that includes the very same type of information currently being collected on the other side of the world -- facial photographs, fingerprints, and iris scans – here in the United States and elsewhere in the Western world. The IBM system, however, comes with the notable addition of voice files.
In regard to the predicted biometric identification technology, IBM states:
You will no longer need to create, track or remember multiple passwords for various log-ins. Imagine you will be able to walk up to an ATM machine to securely withdraw money by simply speaking your name or looking into a tiny sensor that can recognize the unique patterns in the retina of your eye. Or by doing the same, you can check your account balance on your mobile phone or tablet.
Each person has a unique biological identity and behind all that is data. Biometric data – facial definitions, retinal scans and voice files – will be composited through software to build your DNA unique online password.
Referred to as multi-factor biometrics, smarter systems will be able to use this information in real-time to make sure whenever someone is attempting to access your information, it matches your unique biometric profile and the attempt is authorized.
All of this is precisely the argument behind the enormous database being implemented in India, as well as behind the technology being introduced to the American public under the guise of convenience and protection against identity theft. Although the systems have yet to take off culturally, there is little doubt that the vast majority of trendy Americans will be content to give up their most private information to either the government or to greedy corporations (which are now essentially one and the same) based solely on the promise of more convenience and the ability to use even less of their brain during the course of the average day.
But, although many simply remain silent at first, due to the fact that they are currently able to go about their day without encountering such invasive technology, the truth is that their ability to continue to gain access to accounts and pay bills with cash, checks, etc. is fading fast. In totalitarian systems such as our own, what begins as a convenience for those who can afford it almost always ends in compulsion and mandates for everyone, even those at the bottom.
As I stated in my last article, “Cashless Society: India Implements First Biometric ID Program for all of its 1.2 Billion Residents,”
At first, the program is introduced as a way to speed up transactions, increase efficiency, and provide convenience. Soon, however, governments and businesses begin to transition out of the older methods of payment and identification and focus more on the new technology. Identification using the traditional methods remain as an option, but become viewed as cumbersome. Eventually, the alternative methods are phased out completely and mandates replace what was once a personal choice.
[See end of article for more – N.I. Ed]
Equally as frightening as a Cashless Society and biometric ID databases, is the fact that IBM predicts that, within five years, humans will have their brains linked to computers with the ability to control cursors and operate digital systems by thought alone.
The IBM statement reads:
IBM scientists are among those researching how to link your brain to your devices, such as a computer or a smartphone. If you just need to think about calling someone, it happens. Or you can control the cursor on a computer screen just by thinking about where you want to move it.
Scientists in the field of bioinformatics have designed headsets with advanced sensors to read electrical brain activity that can recognize facial expressions, excitement and concentration levels, and thoughts of a person without them physically taking any actions.
Yet, although IBM predicts these inventions as advancements in the near future, the fact is that they already exist, even within the mainstream level of science that is permitted to be disclosed for public consumption. For years implants have allowed monkeys to control computer cursors and even robotic arms in laboratory settings.
In a recent experiment, two macaque monkeys were trained to control a virtual arm represented on the computer screen and use the arm to “grasp” virtual objects, even feeling the objects that they grasped.
Such technology has long been promoted by those in the Singularity movement, a branch of Transhumanism that looks forward to the day when humans actually merge with machines to create a new and “improved” type of human species.
Lastly, IBM’s predictions about harnessing energy, while possibly a positive development in terms of environmentally friendly energy solutions, are also a bit alarming, especially when taken in context of its other developments. IBM states:
Anything that moves or produces heat has the potential to create energy that can be captured. Walking. Jogging. Bicycling. The heat from your computer. Even the water flowing through your pipes.
Advances in renewable energy technology will allow individuals to collect this kinetic energy, which now goes to waste, and use it to help power our homes, offices and cities.
Interestingly enough, “anything that moves or produces heat” includes human beings. While the technology could be used to harness wasted energy and turn that into a truly sustainable method of energy production that can continue to be improved upon, one must also wonder if human beings will not become the focus of the energy output source.
Is it feasible that a human being's natural energy might be used to power some type of computer/brain interface device? Or that a human’s natural energy would be harnessed to power other devices outside of the body? Could this energy be harnessed from afar?
IBM is not clear in its press release as to the potential ethical concerns over its “new” technology. However, with a company that has such an unfortunate history regarding ethical decisions, it might be wise to view its announcement with a large dose of healthy skepticism and reserve.
Although this type of technology, for some, may seem unbelievable, the fact is that it is very real. No longer are computer/brain interfaces something only seen in movies like The Matrix. No longer can the Cashless Society be considered merely the rumination of country preachers and “conspiracy theorists.”
The future is already here. If we are to control our own destiny, it is essential that we recognize the path we are on and whether or not we should proceed more carefully.
Cashless Society: India Implements First Biometric ID Program for all of its 1.2 Billion Residents
By Brandon Turbeville
 |
Over the past few months, I have written several articles dealing with the coming cashless society and the developing technological control grid. I also have written about the surge of government attempts to gain access to and force the use of biometric data for the purposes of identification, tracking, tracing, and surveillance.
Unfortunately, the reactions I receive from the general public are almost always the same. While some recognize the danger, most simply deny that governments have the capability or even the desire to create a system in which the population is constantly monitored by virtue of their most private and even biological information. Others, either gripped by apathy or ignorance, cannot believe that the gadgets given to them from the massive tech corporations are designed for anything other than their entertainment and enjoyment.
However, current events in India should serve not just as a warning, but also as a foreshadowing of the events to come in the Western world, specifically the United States.
Recently, India has launched a nationwide program involving the allocation of a Unique Identification Number (UID) to every single one of its 1.2 billion residents. Each of the numbers will be tied to the biometric data of the recipient using three different forms of information – fingerprints, iris scans, and pictures of the face. All ten digits of the hand will be recorded, and both eyes will be scanned.
The project will be directed by the Unique Identification Authority of India (UIDAI) under the premise of preventing identity theft and social welfare fraud. India has rather extensive social welfare and safety net programs, ranging from medical support and heating assistance to others aimed at helping the poor. Fraud is a rampant problem in India, especially in relation to these programs due to a preponderance of corrupt politicians and bureaucrats who often stuff welfare rolls with fake names and take the money for themselves.
Yet, although the justification for the billion person database is the increased ability to accurately disperse social welfare benefits, it will not be just the Indian government’s social welfare programs that have access to and utilize the UIDAI. Indeed, even before the program has been completed, major banks, state/local governments, and other institutions are planning to use the UIDAI for identification verification purposes and, of course, payment and accessibility.
Yet the UID is going to be used for much more than social welfare programs. The UIDAI is in discussion with many institutions (banks, local/state governments, etc.) to allow them to use the UID as a means of identity verification. These institutions will pay the UIDAI some fee to cover costs and generate revenue. There seems to be little doubt that once it is established, the UID will become a preferred method (if not the preferred method) of identification in India.
Saenz also sees the eventuality of the UIDAI program becoming a means of payment and accessibility. He continues:
Ultimately, I wouldn’t be surprised if the UID, with its biometric data, could be used as a means of payment (when linked to a bank account), or as an access key to homes and cars. Purchase a meal with your fingerprint and unlock your door with the twinkle in your eye. Similar results could be expected in other nations that adopted biometric identification systems.
Saenz, and other proponents of the UID (UIDAI), have been diligent in pointing out that the program “is just a number, not an ID card.” However, this claim is debatable. Saenz himself admits that State issued driver’s licenses and identification cards will reference the UID information.
The question then becomes how much of that information will be referenced, and how that will be accomplished? Will the information be included on the card? Will only part of the information be included on the card? Or will the card reference back to the digital UID information to be then reconciled with the information that is present on the card? Although the UID is obviously going to be utilized by other institutions outside of the social welfare programs, no answers to these questions have been provided.
But, in the end, does it really matter if the information is collated into an ID card format if the government already has access to that information digitally? More than likely, a national ID card will appear as a supplement to the database already created by UID. Regardless, the private biometric information has still been taken from the individual. The database is still there.
Indeed, government “officials” have already stated that the database will be used by intelligence agencies for the purpose of monitoring “bank transactions, cellphone purchases and the movements of individuals and groups suspected of fomenting terrorism.” This will be very easy to do since the UID number will be entered anytime an individual “accesses services from government departments, driver’s license offices and hospitals, as well as insurance, telecom, and banking companies.”
Nevertheless, proponents have also touted the fact that, at this point, the UID program is optional. But the program will obviously not be optional for very long. As I have discussed in previous articles, the introduction of a program such as a national ID card, biometric data, or cashless payment technologies is always followed by the program becoming mandatory. The ultimate goal of an all-encompassing cashless surveillance program with no opt-out provisions is always introduced by stealth and the Gradualist Technique.
At first, the program is introduced as a way to speed up transactions, increase efficiency, and provide convenience. Soon, however, governments and businesses begin to transition out of the older methods of payment and identification and focus more on the new technology. Identification using the traditional methods remain as an option, but become viewed as cumbersome. Eventually, the alternative methods are phased out completely and mandates replace what was once a personal choice.
As soon as Indian banks, businesses, and government social service offices begin to require identification using the UID, the ability to remain off the system and lead what passes for a normal life will disappear.
This is exactly the intention with India’s new biometric ID program. In fact, the cashless society is a stated goal of the UID program. CEO of MindTree’s IT Services, the company that was awarded the government contract for development and maintenance of the UID, explained in an interview with ComputerWeekly that the “ID scheme will support a cashless society. He said all vendors will have a biometric reader and citizens can pay for things with a fingerprint scan. Even a bag of rice.”
No doubt, even after such an admission by a man who was instrumental in the development of the program, many who read this article will still dismiss it as a “conspiracy theory.”
Nonetheless, this new monumental data mining effort by the Indian government dovetails with recent efforts in the Western world to develop an electronic surveillance grid capable of tracking, tracing, and recording every single movement and communication of every single citizen within a nation’s borders.
New technologies which are being introduced inside the United States, the UK, and Australia such as vein scanners, biometric employee time and attendance systems, voice recognition devices, and behavior analysis systems are all geared toward Total Information Awareness of every human being on the planet.
New technologies which are being introduced inside the United States, the UK, and Australia such as vein scanners, biometric employee time and attendance systems, voice recognition devices, and behavior analysis systems are all geared toward Total Information Awareness of every human being on the planet.
Only a totalitarian form of government would desire this information; and only a very determined totalitarian government would actively work toward establishing it. India is only the first nation to openly sweep up its entire national population into such a massive biometric database net. We cannot let our nation be the next.
From Activist Post @ http://www.activistpost.com/2012/01/cashless-society-india-implements-first.html
Brandon Turbeville is an author out of Mullins, South Carolina. He has a Bachelor’s Degree from Francis Marion University where he earned the Pee Dee Electric Scholar’s Award as an undergraduate. He has had numerous articles published dealing with a wide variety of subjects including health, economics, and civil liberties. He also the author of Codex Alimentarius - The End of Health Freedom, 7 Real Conspiracies and Five Sense Solutions. Brandon Turbeville is available for podcast, radio, and TV interviews. Please contact us at activistpost@gmail.com.
From Activist Post @ http://www.activistpost.com/2012/01/beyond-cashless-society-ibms-vision-for.html
Video - http://www.youtube.com/watch?v=51Num5h7itk&feature=player_embedded
Downloading Humans: The Hive Group Philosophy
…The Internet now appears to be enfolding into a tyrannical high-tech control grid. After all, the powerful monopolistic cartels that control every industry, every government, and the media, must feel thoroughly threatened by the Internet -- which, in its current form, represents the ultimate "free market" of free minds where all the people can voice their uniqueness.
According to Wired, Google has partnered with the CIA to fund intricate tracking of the Internet:
According to Wired, Google has partnered with the CIA to fund intricate tracking of the Internet:
The company is called Recorded Future, and it scours tens of thousands of websites, blogs and Twitter accounts to find the relationships between people, organizations, actions and incidents — both present and still-to-come. In a white paper, the company says its temporal analytics engine “goes beyond search” by “looking at the ‘invisible links’ between documents that talk about the same, or related, entities and events.”
Besides the now public merger between Google and the CIA, there is a privately-held, little-known company called The Hive Group, specializing in "decoding the Internet's raw data," which seems to be at the heart of a philosophical high-tech system that seeks to track, trace, and database our every move. The Hive Group was founded by the creator of hyperlink technology, Ben Shneiderman, a computer scientist specializing in human-computer interaction. According to their site they offer, "information treemapping solutions to both industry and government." Their primary commercial product, Honeycomb, is listed as a tool for Armed Services, International Governance and Security, and Intelligence described as:
The company builds Highly Immersive Visual Environments that are deployed in operational intelligence (OI), business intelligence (BI), and complex event processing (CEP) contexts. The company’s treemapping software is the foundation of these visual environments.
Shortly after September 11th, Hive Group founder Dr. Shneiderman testified in Congressional hearings about national identification systems and Biometric ID cards on behalf of the U.S. Public Policy Committee of the Association for Computing Machinery (USACM), which is an 80,000-member strong international professional society, where he said:
Implementing an intricate national identification system is a challenging systems engineering matter. It requires a complex integration of social and technical systems, including humans, hardware, software, networks, and database security. Such socio-technical systems are always vulnerable to error, breakdown, sabotage and destruction by natural events or by people with malicious intentions.
In a 2002 book, Human Choice and Computers: Issues of Choice and Quality of Life in the Information Society, when referring to Biometric ID cards or other National Identification Schemes (NIDS) possibly having prevented the September 11th attacks, the authors quote Shneiderman's testimony, "The positive identification of individuals does not equate to trustworthiness or lack of criminal intent."
In other words, Big Brother has a lot of work to do on predictive behavior technology to keep us safe from the terrorists. Let's now remember that this testimony took place nearly 9 years ago with many billions since spent on the Intelligence Industrial Complex. The Hive Group is one of the companies spearheading the bridge between government and the private sector, having done work for the Defense Department, Lockheed Martin, and SAIC, and even mapped the spread of the bogus H1N1 outbreak "pandemic."
In a rare article (press release) in The Washington Post about the privately-held company, titled "The Next Frontier: Decoding the Internet's Raw Data," Schneiderman is quoted as saying:
In a rare article (press release) in The Washington Post about the privately-held company, titled "The Next Frontier: Decoding the Internet's Raw Data," Schneiderman is quoted as saying:
Our belief is that technology is not just useful as toys or for business, we're talking about using these technologies for national priorities.
Although the majority of HIVE's commercial applications seem somewhat benign, the "national priorities" he refers to lean more toward tyrannical control than actual cybersecurity.
The company also has a nefarious connotation with its acronym HIVE and its key product Honeycomb. Both concepts are derived from Transhumanism -- the philosophy to culturally self-direct evolution and facilitate the human-computer bond into a scientific dictatorship modeled after the central direction of the beehive colony in nature. It should be no surprise, then, that The Hive Group offers a world population application, since Julian Huxley -- the father of Transhumanism -- was instrumental in the philosophy and policies of population management and reduction.
We are heading toward an age where mind and machine are one and the same. For the advocates of freedom, it is a true blessing to be able to congregate and disseminate the message of peace and prosperity. However, under the authoritarian rule of the control-oriented HIVE philosophy -- where man is no better, nor different, than bees in a honeycomb -- we have been reduced to be workers at the service of the queen.
The company also has a nefarious connotation with its acronym HIVE and its key product Honeycomb. Both concepts are derived from Transhumanism -- the philosophy to culturally self-direct evolution and facilitate the human-computer bond into a scientific dictatorship modeled after the central direction of the beehive colony in nature. It should be no surprise, then, that The Hive Group offers a world population application, since Julian Huxley -- the father of Transhumanism -- was instrumental in the philosophy and policies of population management and reduction.
We are heading toward an age where mind and machine are one and the same. For the advocates of freedom, it is a true blessing to be able to congregate and disseminate the message of peace and prosperity. However, under the authoritarian rule of the control-oriented HIVE philosophy -- where man is no better, nor different, than bees in a honeycomb -- we have been reduced to be workers at the service of the queen.
From Activist Post @ http://www.activistpost.com/2010/07/downloading-humans-hive-group.html
Please Help Keep This Site Online
Donate any amount and receive at least one New Illuminati eBook!
For further enlightening information enter a word or phrase into the search box @ New Illuminati or click on any label/tag at the bottom of the page @ http://nexusilluminati.blogspot.com
And see
The Her(m)etic Hermit - http://hermetic.blog.com
New Illuminati – http://nexusilluminati.blogspot.com
New Illuminati on Facebook - http://www.facebook.com/pages/New-Illuminati/320674219559
This material is published under Creative Commons Fair Use Copyright (unless an individual item is declared otherwise by copyright holder) – reproduction for non-profit use is permitted & encouraged, if you give attribution to the work & author - and please include a (preferably active) link to the original along with this notice. Feel free to make non-commercial hard (printed) or software copies or mirror sites - you never know how long something will stay glued to the web – but remember attribution! If you like what you see, please send a tiny donation or leave a comment – and thanks for reading this far…
From the New Illuminati – http://nexusilluminati.blogspot.com


I'd much rather just type my passwords in manually than become a permanent fixture of the matrix thank you very much IBM...
ReplyDeleteYour comment makes us wish there was a 'like' function for comments here, I.A.!
ReplyDeleteNSDL Pan
ReplyDeleteApply For Lost Pan
apply for aadhar card
aadhar card status online
Nice Post.Thanks for sharing wonderful information about Customer Loyalty and for more information about Cashless Payments and Digital Customer Loyalty in detail visit
ReplyDeleteDigital Loyalty Program | Cashless Payments
JOIN THE GREAT ILLUMINATI BROTHER HOOD TODAY AND LIVE A BETTER AND HAPPY LIFE. WELCOME TO THE GREAT TEMPLE OF RICHES,FAME AND POWERS. Are you a business,Man or woman, politician, musician,pastor,lawyer,actor,actress,banker, and you. want to be rich, powerful and be famous in life. You can achieve your dreams by being a member of the Great ILLUMINATI brother hood. With this all your dreams and heart desire can be fully accomplish, if you really want to be a member of the great ILLUMINATI brother hood, Note: newly recruited members are entitled with$1,000,000.00 USD , A Golden Ring, that will protect and guild you from enemies, and a free visa to United State Of America . Please will do not share blood. Kindly email us on illuminatiofficial005@gmail.com or illuminatiofficial0088@yahoo.com
ReplyDelete